Cybersecurity and Managed IT Services for Oklahoma Businesses
Reduce your cyber risk in 90 days with proactive protection, always-on monitoring, and real-world defense strategies
How Do We Reduce Cyber Risk?
Cybersecurity
Proactive protection that stops cyber threats before they impact your business.
Cyber Liability
Financial protection that helps your business recover quickly after a cyber incident.
Managed IT Services
Reliable IT management that keeps your systems secure, stable, and supported.
Your Path to Protection
1. Risk & Liability Assessment
We start by understanding your business, your data, and your exposure. This includes a high level security review and a real conversation about liability, compliance, and what a breach would actually mean for you.
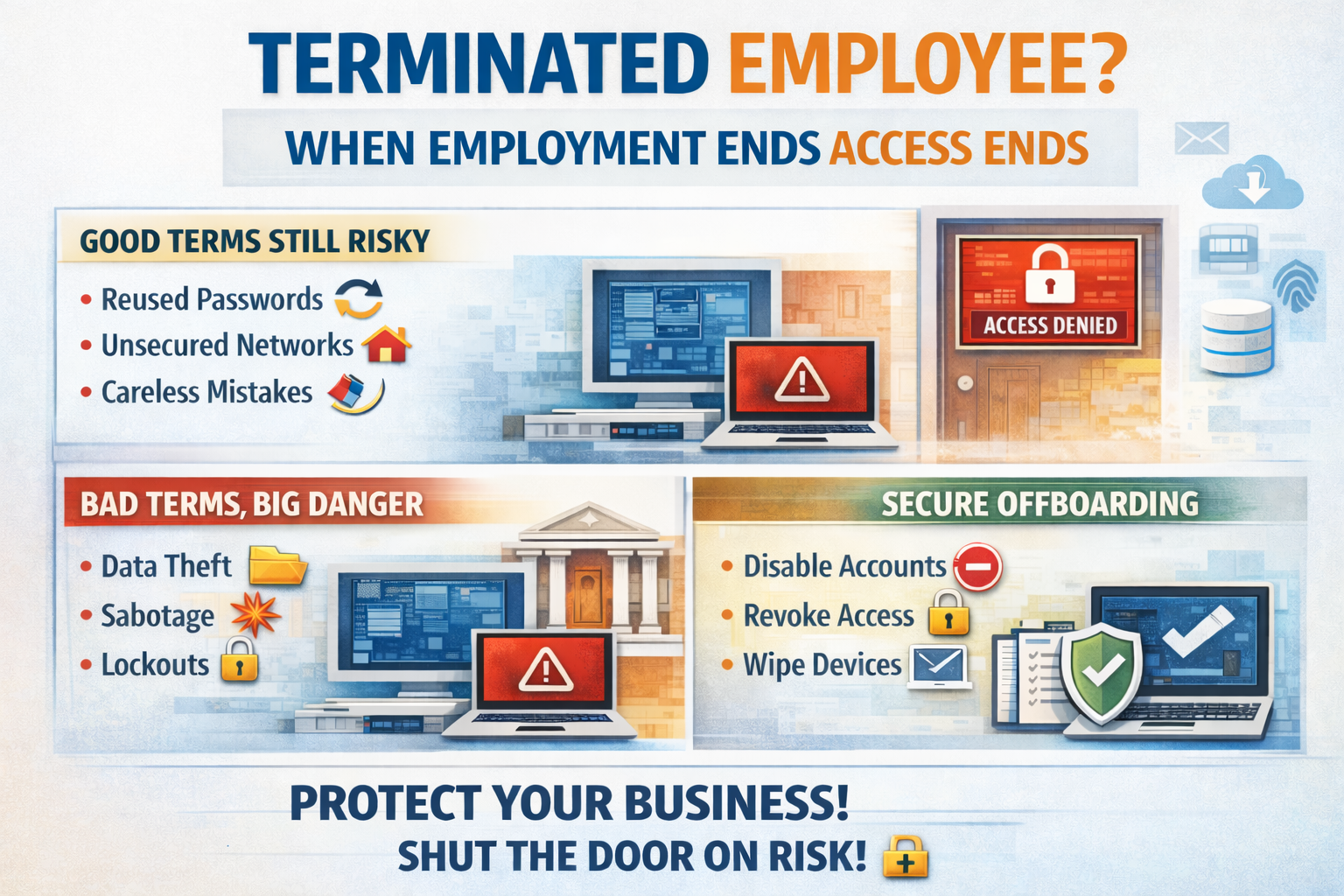
2. Vulnerability Discovery
Next, we identify the gaps. From email and endpoints to network and user behavior, we uncover where attackers would strike first and how they would get in.
3. Security Strategy & Roadmap
No cookie cutter solutions. We build a security plan tailored to your risk level, budget, and business goals, prioritizing what protects you the fastest and reduces liability the most.
4. Protection Deployment
We implement layered defenses across email, endpoints, networks, identities, and users. This is where real protection goes live and weak points get locked down.
5. Ongoing Monitoring & Hardening
Security is never set it and forget it. We continuously monitor, alert, train users, and strengthen defenses as threats evolve, keeping you protected long term.
I lose sleep so you don’t have to.
While you are running your business, serving customers, and trying to grow, cyber threats do not stop. Hackers do not care how small your company is or how busy your day gets. That is where I come in.
My job is simple. Worry about cybersecurity so you can focus on everything else. I obsess over threats, vulnerabilities, and weak points before attackers can exploit them. I believe businesses deserve real protection, not buzzwords, and security that actually works in the real world.
If you rely on email, data, or technology to run your business, you are already a target. You do not have to face that risk alone.
Let’s find out where you stand and what needs to be fixed.
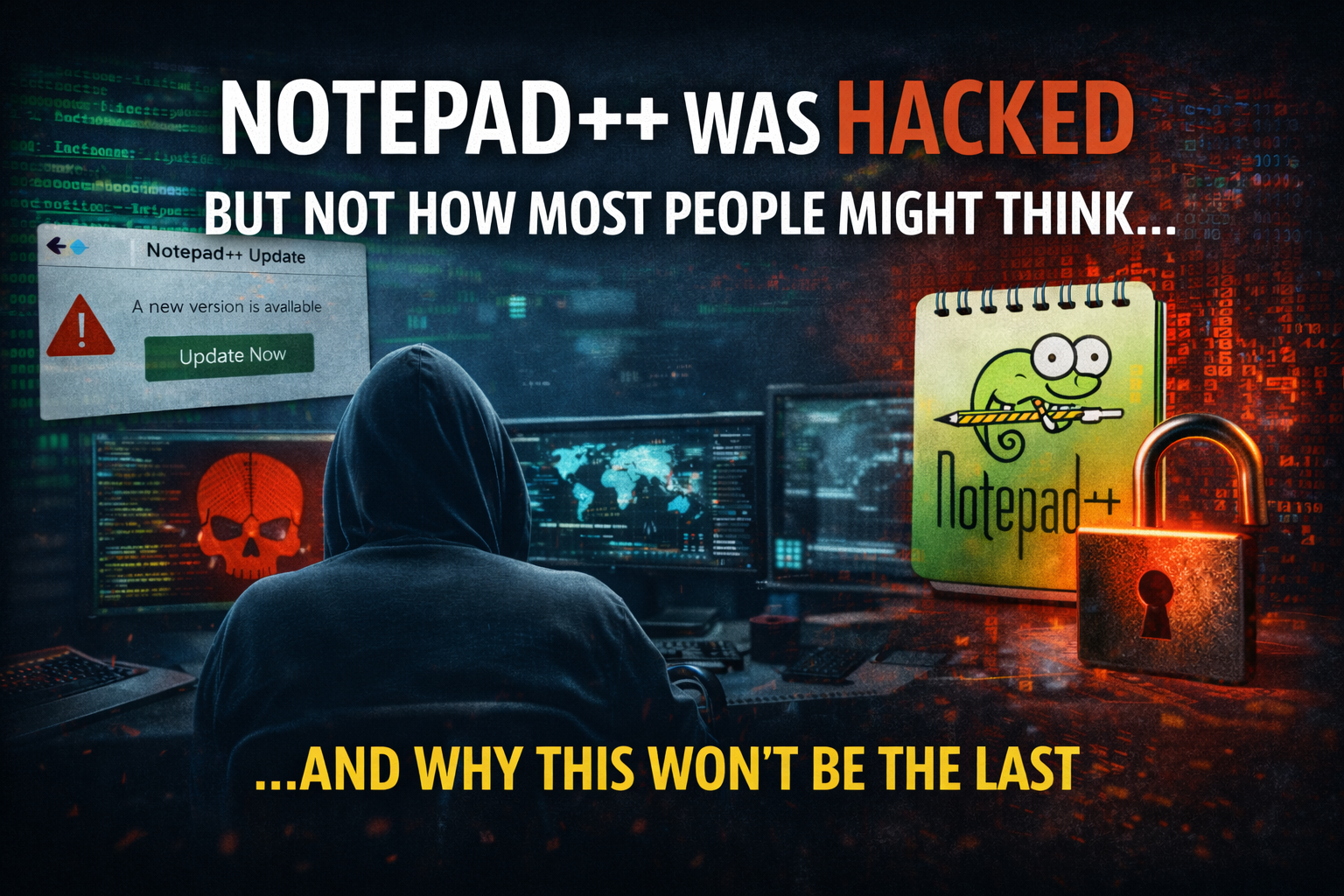
Latest from Our Blog
To stay ahead of cyber threats, our team shares tips and updates on cybersecurity and IT topics. Check out our latest insights to enhance your cybersecurity measures.
Blog Posts